For Excel documents to work with different versions and browsers, the MIME type must be set correctly. In-depth handling of MIME types such as application/vnd.ms-excel and application/vnd.openxmlformats-officedocument.spreadsheetml.sheet is covered in this article.
Java - Temporary e-mail blog !
Dive into the world of knowledge without taking yourself too seriously. From the demystification of complex subjects to jokes that defy convention, we're here to rattle your brain and bring a wry smile to your face. 🤓🤣
This tutorial explains how to use JUnit to test Java inner classes, private methods, and fields. It tackles the difficulties of upholding encapsulation while guaranteeing exhaustive testing.
Significant performance differences are observed while generating 1000x1000 matrices in Java with the characters 'O' and '#' or 'O' and 'B'. While the second matrix takes 259.152 seconds to complete, the first matrix does it in 8.52 seconds. This disparity results from the way the Java console handles various characters; rendering takes longer when 'B' is used.
In Android, maintaining the state of an activity is essential to guaranteeing a flawless user experience. Developers can store UI states and get them upon reproduction of an activity by using the onSaveInstanceState method.
Java methods like Integer.parseInt and Integer.valueOf, which are crucial for data processing and input validation, are involved in converting a string to an integer. Using try and catch blocks to handle exceptions and guaranteeing performance efficiency for large-scale conversions are examples of advanced approaches.
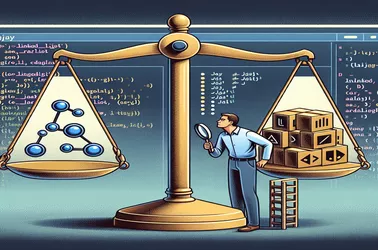
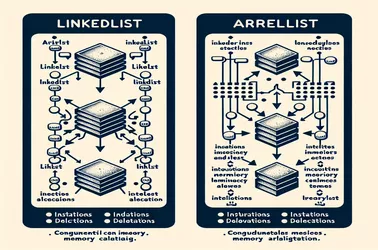
The differences between ArrayList and LinkedList in Java are covered in detail in this guide. ArrayList performs well in situations where quick random access is needed, but it is not as well suited for frequent changes. In contrast, LinkedList has a larger memory overhead but performs exceptionally well in applications that require efficient insertions and deletions.
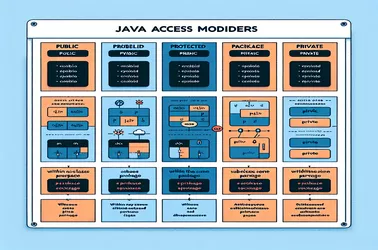
Class members' visibility and accessibility are controlled using Java access modifiers. Package-private, public, protected, and private are the modifiers that are most important for encapsulation and inheritance.
Several ways to initialize a ArrayList in a single line are covered in this guide. We present a comparative study of more contemporary methods like Arrays.asList, List.of, and bespoke utility methods, and classic multi-step procedures. Each strategy is well explained, emphasizing its advantages and applications.
This article looks at the significance of serialVersionUID in Java serialization and explains how it keeps a Serializable class compatible across versions.
In Java, there are multiple techniques for converting a string to an integer, such as Integer.parseInt() and Integer.valueOf(). These techniques are simple and effective for simple conversions. The Scanner class or third-party libraries such as Apache Commons Lang can be used for more resilient handling.
This tutorial tackles the problem of sluggish Android emulator performance on an x86 Windows XP Professional computer with a 2.67GHz Celeron processor and 1.21GB of RAM. The emulator is still slow even after following the IDE, SDK, and JDK setup instructions.
The contrasts between LinkedList and ArrayList in Java are explained in this guide, along with an emphasis on their respective advantages and suitable usage situations. Knowing when to use each can make a big difference in how well your apps operate and use memory.
A crucial design pattern in software engineering that improves testability and maintainability of programs is dependency injection. Decoupling components enhances code modularity and makes managing dependencies easier. Dependency injection comes in a variety of forms, each with specific advantages and applications, such as constructor, setter, and interface injection.
The nuances of the Java access modifiers, public, protected, package-private, and private, are explored in detail in this article. When it comes to regulating the accessibility and visibility of classes, methods, and variables, each modifier has a distinct function. Maintaining clean, modular code and successfully encapsulating ideas requires an understanding of these distinctions.
Java's implicit type conversions are handled using compound assignment operators such as +=, -=, *=, and /=, which make code simpler. These operators carry out the required conversions internally, as contrast to straightforward assignments that call for explicit casting.
Optimizing efficiency in a Java Map requires efficiently iterating over each entry. distinct approaches have distinct benefits, such as the for-each loop, Streams API, Iterator, and the forEach technique.
The hilarious intent of the wacky method isUserAGoat() in the Android 4.2 API can be discovered by investigating it. By determining whether a user is a goat, this technique gives the platform a hint of developer comedy.
One common operation that improves flexibility and data manipulation in Java is to convert an array of elements to an ArrayList. Developers can accomplish this conversion quickly by using Java Streams and Arrays.asList() methods.
In Java, there are multiple ways to generate random integers inside a range while avoiding typical issues like integer overflow and erroneous ranges. By employing classes like as Random, SecureRandom, and ThreadLocalRandom, developers may guarantee precise and safe creation of random numbers.
This article examines the key differences between HashMap and Hashtable in Java and assesses how well they perform in non-threaded applications.
GetSystemService and hideSoftInputFromWindow are two programmatic ways to hide the Android soft keyboard. These can be used in conjunction with touch and click listeners to effectively control keyboard appearance and improve user experience.
This tutorial examines several methods for avoiding NullPointerException in Java. It describes how to utilize the Null Object Pattern to provide default behavior, @NonNull annotations to enforce null safety at build time, and Optional to handle null values gracefully.
The problem of the Java extension code runner in Git Bash within VS Code not being able to execute a program twice is discussed in this article. It explores possible explanations such as environmental setup and command handling. We provide workable techniques to guarantee the software functions well by offering a batch script and an example Java program.
A key tool in software development for validating input data and making sure it follows anticipated formats are regular expressions (regex). This procedure is essential for lowering errors and enhancing system security.
Catering to overseas clients requires setting up localized date headers in SMTP messages to ensure that time-sensitive communication adheres to local customs. To address the time zone difference between the server and the recipient, locale-specific date formats can be used with modifications to the SMTPMessage headers.
When utilizing Jakarta Mail with a Gmail account, handling attachments in automated mail systems frequently results in messages being tagged as spam. Assuring appropriate content for management and sender reputation, as well as installing authentication measures like SPF and DKIM, are some strategies to increase deliverability.
Flamegraph, an Apache Flink tool, does not natively provide alert alerts like alerts. Custom integration with monitoring APIs is necessary to accomplish this. By employing these APIs, developers can establish thresholds for crucial performance measures to initiate alerts, guaranteeing prompt resolution of possible problems in the system's architecture.
In-app purchases are frequently impacted by customers clearing all data from the Google Play Store in an attempt to resolve problems, which frequently resets the default account. Purchases made under the user's original account may no longer be recognized as a result, causing a disparity.
Examining the intricacies of utilizing Java with Amazon SES V2 highlights the common problems and mistakes that arise, like incorrect handling of exceptions and configuration mistakes. These problems can be considerably reduced by comprehending the underlying architecture of AWS services and putting best practices into Java.
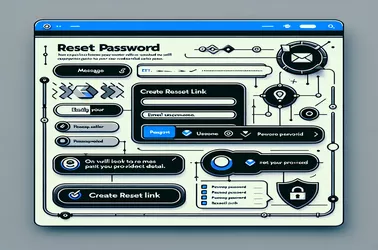
Using the admin API of the platform to register users and distribute secure, customized links via a custom messaging service is the process of creating a custom password reset link for Keycloak. The solution makes use of a particular token generation technique to guarantee that the link is active until it is used. By addressing typical problems such as token expiration, password recovery methods become more dependable and safe, improving user experience.
A multifaceted approach is needed to address the problem of duplicate registrations in Java online applications. Developers need to apply complete tactics, ranging from optimizing frontend interactions for improved user feedback to integrating backend checks to assure uniqueness of user data.
It is essential to refactor Java regex patterns for validation in order to improve application security and performance. The necessity for efficient code execution is highlighted by the emphasis on optimizing the regex to prevent stack overflow errors with huge inputs. Furthermore, validating user inputs and ensuring the application's resistance against potential risks are ensured by updating regex to the latest email standards.
Adding the capability to send notifications emails straight to users' inboxes to Java applications can greatly improve the functionality and user experience of software.
This text explores the nuances of employing regular expressions to maintain input integrity, starting with Java strategies for data validation.
Compound assignment operators in Java, like +=, -=, *=, and /=, make coding simpler by integrating assignment and arithmetic operations in one step.
For developers, the ability to generate random integers within a given range in Java is essential since it allows for the creation of dynamic and surprising behavior in programs.